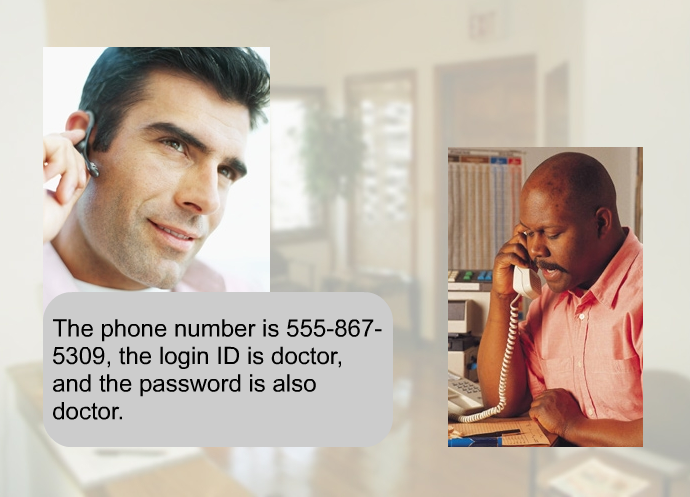
Social engineers get useful information from unsuspecting people and use it in potentially nefarious ways. Simple conversations provide the opportunity for the social engineer to get seemingly benign information from individuals over the course of one or many encounters. That information can then be combined with other open source information to then provide the social engineer with everything they need to carry out an attack on a system, enter a secure building, or any number of applications that could cause harm to your organization.
Protect your employees by educating them about the direct implications this can have on your company. Teach them what to look for so they can avoid falling prey to this kind of tactic. Provide access to this CBT (computer based training) which is a short video (6:40) telling them about a scenario where a fraudster gets an employee to give him the login and password of their billing system over the phone. There is no need to create a complicated hack into a system when an employee unwittingly hands that information over to the social engineer. At first glance, you may think, “My employees would never fall for that,” but when you can see and hear what happens in this example, you will soon realize how vulnerable your organization actually is.
Use this social engineering CBT for your global antifraud program as part of the fraud awareness training and governance (compliance) components. It will directly benefit your InfoSec (information security) efforts in I.T. as well as start the conversation about other possible vulnerabilities within your company.
The CBT content is based on the Social Engineering chapter
with permission from the author in the book “No Tech Hacking.”
Find out how this could happen.
Educate your employees and prevent this from happening in your organization.